This is Part 3 of a pre-print draft of Chapter 6 from Smart Things: Ubiquitous Computing User Experience Design, my upcoming book. (Part 1) (Part 2)The final book will be different and this is no substitute for it, but it's a taste of what the book is about.
Earlier chapters in this series: Chapter 3, Chapter 1Citations to references can be found here.
Chapter 6: Information shadows
Part 3: Point-at things
Systems of information shadows are created by promoting standard methods for associating a physical object and information about it. Experience designer Tom Coates coined the term point-at things while compiling ways to organize BBC's program directory. [Footnote: See (British Broadcasting Corporation, 2000) for the information architecture standard the BBC produced as part of the process described in this section.] In that project, he realized that "once you [uniquely identify] a programme episode then something really significant happens—you can give it a name, make it addressable, you can—for the first time point at it. Better still, you can move from pointing at something to glueing handles onto it. And once you have such a handle, then you can pick up the programme and throw it around and stick labels on it and join it together with other programmes." (Coates, 2004) [The original post.]
[Footnote: A similar term to point-at things is Bruce Sterling's spime, a neologism that merges space and time, because those are two key data points in an object's identity. As Sterling puts it, "every object worthy of human or machine consideration generates a small history. These histories are not dusty archives locked away on ink and paper. They are informational resources, manipulable in real time. […] The key to the spime is identity. A Spime must therefore be a thing with a name. No name, no spime." (Sterling, 2005)]
His realization, which translates directly to organizing information shadows, is that when a unique identifier is attached to an object, it becomes possible to collect the metadata about that object into a single information shadow. That unique identifier is the leverage point with which to access and manipulate the whole information shadow in relation to similar shadows.
For example, when the online retailer Amazon branched out from selling books to selling other kinds of products, they needed a way to identify every item they sold. Extending the International Standard Book Number (ISBN) they were already using, they created the Amazon Standard Identification Number (ASIN) to uniquely identify every product they sell. This allowed all of the items they sell to become, in Coates' term, point-at things. It became possible to precisely identify exactly which product was being linked, discussed, etc. That precision allowed for a wide degree of flexibility and power—which other services could use to build upon Amazon’s inventory systems. As of late 2009, ProgrammableWeb.com lists more than 300 services that use Amazon's ASIN system to create additional services. [Footnote: Using Amazon's eCommerce API.] Pickii, for example, uses ASINs, Amazon's list of categories, and user ratings for individual products to create a top-10 best-reviewed list for virtually every Amazon product category.
Matt Biddulph, one of Coates' colleagues at the BBC, and Ulla-Maaria Engeström (née Mutanen) took this idea further. While useful, Amazon's ASIN was limited to products Amazon sold. What about the "many small producers especially in developing countries do not have access to create unique identifiers, and therefore, their products are not equally visible or recommendable online" (Biddulph and Mutanen, 2006)?
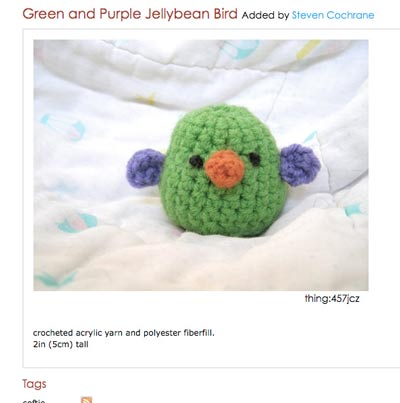
Figure 6-6. Unique item on Thinglink, showing Thinglink ID in the lower right-hand corner of the photo
In response to this observation Mutanen created Thinglink, "a service where anybody can register unique identifiers for objects that they want to identify as unique." The service generated a unique alphanumeric identifier (Figure 6-6), and served as the metadata clearinghouse to "aggregate online discussion around particular objects, track the history and transformation of objects, [and] socialize around particular objects." (Biddulph and Mutanen, 2006) In other words, Thinglinks were designed to create point-at-things out of any object by using user-generated unique identifiers to connect single items to their information shadows. [Footnote: As of the end of 2009, the service is still running at thinglink.com, but has shifted its focus from products created by small producers to high design objects.]
When data network access seems almost everywhere, the movement of information about objects within groups of people then intersects with their physical movements. Friends' recommendations, for example, can affect buying choices and preferences, while purchasing an object creates a data event that feeds up through the store's inventory, to the distributor's, all the way back to the manufacturer. Along the way, humans and automated systems make decisions that affect what happens to the object, whether the object is bought, sold, gifted, destroyed, or perhaps refurbished, extending the object’s social life.

Figure 6-7. Nokia 3220 with the NFC shell, the first mass markt mobile phone with a built-in RFID reader (Courtesy Nokia)
As optical identifiers, such as 2D barcodes, become more popular and devices such as the RFID reader on the Nokia 3220 (Figure 6-7) become inexpensive, this symmetry means that nearly everything can be uniquely identified on the cheap. [Footnote: At the time of writing, late 2009, there are more than 60 barcode and 2D barcode scanners in Apple's iPhone App Store.] Coates initially used point-at things to refer to digital objects, but it may soon be common to literally "point at things" to access their information shadows.
Tomorrow: Chapter 3, Part 4: The Internet of Things